Let’s start with a hypothetical situation that can become true at any moment.
Imagine a startup called “FinTechSolutions” that decides to outsource the development of a cutting-edge FinTech mobile app to a team of dedicated developers from an external software company, “CodeCrafters.” The developers from CodeCrafters worked diligently on the project and created a unique algorithm for budget forecasting that became a central feature of the app.
After a while, FinTechSolutions finds out about the application with the same algorithm released by CodeCrafters. Startup initiates the lawsuit, but CodeCrafters argues that their team developed the algorithm and should be considered their intellectual property. The biggest mistake is that FinTechSolutions and CodeCrafters needed to establish an explicit, written agreement regarding intellectual property ownership during the app development process.
In order not to face adverse consequences, we are going to dive into the concept of intellectual property and the peculiarities of its ownership.
Table of Contents:
The Concept of Intellectual Property
The concept of intellectual property boils down to protecting the creative stuff that comes out of our minds – things like inventions, artistic works, brand names, sleek designs, and, most importantly for us, software.
The ways of protecting intellectual property rights have evolved with technological advancements. For example, methods such as automatic answering systems based on machine learning and semantic recognition are being widely used.
Dedicated developers often work on projects owned by clients that can raise questions about ownership of any code or work produced.
Forms of Intellectual Property
It includes various forms of rights: patents, copyrights, trademarks, and trade secrets.
Patent
Patents protect new inventions.
A patent is a legal right granted to an inventor by the government, giving the inventor exclusive rights to make, use, and sell an invention for a certain period, usually 20 years from the filing date. In exchange for this exclusive right, the inventor must publicly disclose the details of the invention.
Trademark
Trademarks allow businesses to distinguish themselves in the market.
A trademark is a form of intellectual property used to protect a brand’s identity and prevent others from using similar marks that could confuse consumers. It can be a visual symbol such as a word, name, device, label, numerals, or combination of colors.
Trademark laws vary in countries and regions. For example, trademarks can be registered with the U.S. Patent and Trademark Office (USPTO) and indefinitely last if renewed periodically. Trademarks are property rights derived from and appurtenant to a commercial enterprise’s goodwill.
Copyright
Copyright safeguards creative works.
Copyright is a form of intellectual property that grants creators of literary, dramatic, musical, and artistic works the rights of reproduction, communication to the public, adaptation, and translation of their work.
For example, copyright protection typically lasts for the author’s life plus 70 years in the United States.
Trade Secret
Trade secrets cover confidential know-how.

Trade secrets are a form of intellectual property companies use to protect confidential information from competitors. They are the most suitable and robust approach to protecting IP for startups in software, biotechnology, medical devices, and hardware industries.
However, unlike patent and copyright laws, trade secret laws lack clear limiting doctrines that consider the social benefits of unauthorized use. Trade secrets can be combined with patents to manage intellectual assets efficiently.
Fortunately, unlike patents, trade secrets do not have a specific expiration date and can remain protected as long as the information remains confidential.
Protection of Intellectual Property
There are various methods and approaches to protecting intellectual property, but most of them can be sorted into two large groups: legal and technical.
Legal Protection
Legal ways to protect intellectual property can include:
Registration
Register your IP with a government agency to safeguard your rights and discourage infringement. For instance, you can secure your patent by registering it with the United States Patent and Trademark Office (USPTO), granting you the rights to produce, use, and sell your invention or utilize the trademark in business transactions.
Licensing
Licensing your IP to others can be a way to generate revenue and expand your reach. For example, you can grant a license for your patent to a company in manufacturing your invention. Similarly, you can license your trademark to a company seeking to incorporate it into their products or services.
Non-disclosure agreements
Non-disclosure agreements (NDAs) can be used to protect your trade secrets and other confidential information. NDAs should be signed by anyone with access to your confidential information, such as employees, contractors, and business partners.
Copyright Notices
Copyright notices serve as an alert to the public regarding ownership rights of copyrighted works. Although not mandatory, they can act as a deterrent against copyright infringement.
Contracts
Contracts can be used to protect your IP rights in various ways. For instance, you can enter into contracts with manufacturers that explicitly prohibit them from disclosing trade secrets. You can also consider entering into an agreement with a distributor responsible for selling your products using your brand name.
Litigation
If someone violates your intellectual property rights, you have the option to take them to court and seek compensation. Your instant reaction will strengthen your reputation as a company with strict policies towards intellectual property ownership and frighten away possible fraudsters.
Technical Means
Intellectual property (IP) is a valuable asset for businesses, and protecting it is crucial to maintaining a competitive edge in the market. While legal measures play a significant role in safeguarding IP, companies also need to implement technical means to ensure its security.
Encryption locks down data.
Robust encryption encoding keeps communication, storage, and databases securely encoded, protecting sensitive information from prying eyes. Encryption transforms data into an unreadable format, making it inaccessible to unauthorized individuals.
Access controls grant permission.
Role-based access management and multi-factor authentication only allow authorized personnel to access intellectual property after multiple verifications.
Secure practices prevent vulnerabilities.
Adhering to safe coding standards and regularly auditing for weaknesses protects software from infiltration or tampering.
Digital signature shows origin.
Embedding identifiers discreetly flags original content, deterring unauthorized distribution by leaving a traceable signature.
Version control provides context.
Implementing version control systems allows businesses to track changes made to their software code. Tracking code modifications over time maintains a record to reference in disputes or catch unauthorized tampering.
Secure transfer protects files.
Secure File Transfer Protocol (SFTP) and encrypted email services provide a secure means of transferring files, protecting them from unauthorized access or interception, and keeping sensitive materials confidential during transportation between parties.
Intrusion Detection and Prevention Systems (IDS/IPS).
Implementing IDS/IPS solutions helps detect and prevent unauthorized access attempts or cyberattacks. These systems monitor network traffic, identify suspicious activities, and proactively mitigate potential threats.
Secure Cloud Storage
Many businesses rely on cloud storage services for data storage and collaboration. Data encryption at rest and in transit, along with strong access controls, can help safeguard intellectual property stored in the cloud. Additionally, hosting data in regions with solid IP protection laws adds an extra layer of security.
Data Loss Prevention (DLP)
DLP tools help monitor and prevent the unauthorized transfer of sensitive information outside an organization’s network. These tools can detect and block attempts to share or leak intellectual property, ensuring its confidentiality. DLP is the most common approach with remote teams of dedicated developers.
Secure Collaboration Tools
These tools should offer encryption and access controls, enabling secure sharing and collaboration while protecting the confidentiality of the intellectual property.
Open Source Intelligence (OSINT) Monitoring
Monitoring online sources and forums for any unauthorized sharing or discussions related to intellectual property is crucial. Trustworthy dedicated developers agree to work under this condition since there is nothing to hide.
Network security blankets the wires.
Firewalls, monitoring, and updated access protocols shield valuable information transmitted through networks from cyber risks.
Best Practices of IP Protection
Non-Disclosure Agreements (NDAs)
Having developers sign NDAs legally binds them to keep your project details and innovations private. This ensures code and ideas stay safely yours.
Source Code Escrow
Іtoring source code with a trusted third party gives peace of mind if issues arise – you can still access vital information. Outsourcing doesn’t mean relinquishing ownership.
Obfuscation
Making code and algorithms challenging to decipher reduces the risks of copying if sharing externally. Protecting trade secrets maintains competitive advantages.
Intellectual Property Management Software (IPMS)
IPMS software helps companies track and manage their intellectual property assetsю. It can also help companies automate patent renewal and trademark filing tasks. Here are three of the best IPMS software options:
DocketTrak
DocketTrak is an advanced patent trademark docketing software that helps organizations manage their intellectual property (IP) assets. It provides automated reminders, customizable reports, DocketForm technology, MyUSPTO.gov and Patent Center integration, built-in rules, trademark update service, a cloud-based, user-friendly interface, mobile accessibility, and affordable pricing.
DocketTrak is a reliable and efficient solution for managing IP assets, suitable for law firms, corporations, and universities. It streamlines IP management processes, provides real-time information, and automates critical tasks, ensuring compliance with IP regulations and never missing important deadlines.
PatentRenewal.com
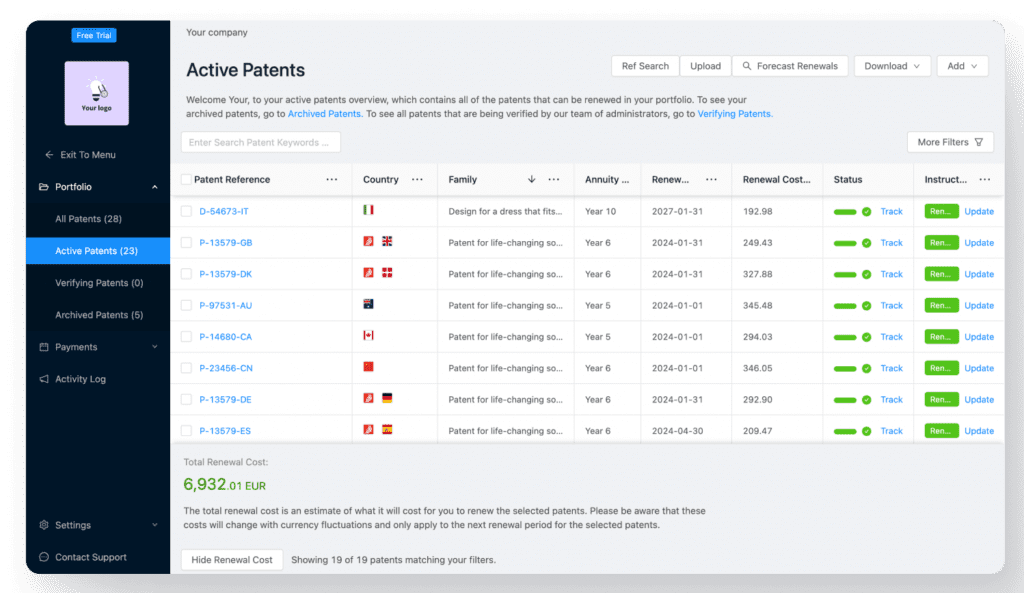
PatentRenewal.com is an online service that helps companies automate the patent renewal process. It also provides features for tracking patent deadlines, managing patent portfolios, and generating reports.
Alt Legal
Alt Legal is a legal technology company that provides a variety of services, including IPMS. Their IPMS platform helps companies track and manage their IP assets, including patents, trademarks, copyrights, and trade secrets.
Digital Rights Management (DRM) Software
DRM software helps companies protect their digital content from unauthorized access and distribution. It can be used to encrypt content, control access to content, and prevent unauthorized copying and distribution of content. Here are three of the best DRM software options: Vitrium Systems, Digify, and PallyCon.
Which Software is Right for You?
The best IPMS and DRM software for you will depend on your specific needs and requirements. Consider the following factors when choosing a software solution:
- The type of IP assets you need to manage: Do you need patents, trademarks, copyrights, trade secrets, or all of the above?
- The size and complexity of your IP portfolio: How many IP assets do you have? How complex are your IP assets?
- Your budget: How much can you afford to spend on IPMS and DRM software? Your ease-of-use requirements: How easy to use does the software need to be?
Сompare the features and pricing of each of the software solutions listed above to choose the best one for your company’s needs.
Background Check of Contractors and IP Due Diligence
Verifying contractors’ credentials, rights, and reputations screens for trustworthiness before collaborating. Due diligence gives confidence that work is in good hands.
Licensing Agreements
Agreements specifically state how intellectual property will be used, modified, and shared clearly. Clarifying rights avoids confusion down the line.
Consulting with Legal Experts
Consulting attorneys experienced in contracts and intellectual property guide strong agreement drafting and customized safeguarding strategies tailored for partnerships.
Business Case: Google vs. Oracle
Let’s delve into a real-life example of an intellectual property conflict: the case of Google vs. Oracle.
Google had incorporated elements of Java, specifically the application programming interfaces (APIs), into Android without obtaining a license from Oracle. Google argued that APIs should not be subject to copyright protection as they are essential for software interoperability.
The consequences for Google were significant. Oracle initially sought $9 billion in damages, although the final amount awarded was reduced.
How It Could Have Been Avoided
Licensing Agreement: Google could have avoided the conflict by entering into a licensing agreement with Oracle to use Java in Android. Paying for the necessary licenses would have provided legal protection and avoided the copyright infringement claims.
What Oracle Did Right in Terms of IP Protection
Clear Ownership: Oracle’s strong case hinged on its clear ownership of Java. They were able to demonstrate that Google had used Java without proper authorization.
Legal Action: Oracle took decisive legal action to protect its intellectual property when it believed it had a case. This proactive approach demonstrated their commitment to safeguarding their IP.
Persistence: Despite initial setbacks, Oracle pursued the case through multiple trials and appeals, eventually securing a favorable ruling. This persistence underscores the importance of defending IP rights.
The Google vs. Oracle case revolved around Google’s use of Java without proper authorization, leading to copyright infringement and patent violation claims. Oracle’s apparent ownership of Java and its proactive legal action brought them a victory.
So, what can we learn from this? Companies should ensure they have licensing agreements and follow intellectual property laws when using third-party software or APIs to avoid such conflicts. It’s just not worth the risk of getting into a legal battle!
How Lengin Guarantees Intellectual Property Safety
Lengin has delivered over 200 projects, each with a unique concept and functionality. Throughout all years of successful collaboration, Lengin’s partners have never faced intellectual property disputes or any security issues. So, what is the secret?
We start any partnership by signing a non-disclosure agreement that considers all client’s concerns, needs, and suggestions. Legal experts check all legal documents to prevent further issues.
Our developers are trustworthy and elaborately vetted, so their diligence and commitment to the contract terms are unquestionable. Before giving access to the new employee, Lengin obligates them to sign all necessary documents to ensure the non-disclosure of trade secrets and any sensitive information about clients and projects.
Conclusion
Navigating intellectual property ownership with dedicated developers is a complex but vital aspect of modern business. While outsourcing software development can provide significant benefits, it also poses risks to intellectual property.
Balancing the advantages of outsourcing with the need to safeguard your intellectual property requires a strategic approach:
- Establish clear contractual agreements.
- Define ownership rights.
- Protect sensitive information through non-disclosure agreements and secure development environments.
Careful planning and legal protections allow leveraging dedicated developers effectively while safeguarding your intellectual property.